Hook, Line, and Sinker: 10 Reasons to Be Alert About Phishing and the Power of Automated Testing and Training
1. Personal Information Theft: Your Identity on the Line
Phishing attacks can steal your personal information, opening doors to identity theft. Automated testing and training can be the vigilant guard against this invisible theft.
2. Financial Loss: Dollars Down the Drain
3. Corporate Secrets Exposed: Business on the Brink
4. Legal Liabilities: The Lawsuit Lurking Around the Corner
5. Reputation Damage: Trust Eroded
6. Targeted Attacks: Spear Phishing’s Sharp Edge
7. Security Systems Bypassed: The Trojan Horse
8. Time and Resource Drain: The Hidden Cost
Recovering from a phishing attack is time-consuming and costly. Prevention through testing and training is an investment that pays dividends in peace of mind.
9. Remote Work Vulnerabilities: The Home Office Trap
10. Complacency: The Silent Enemy
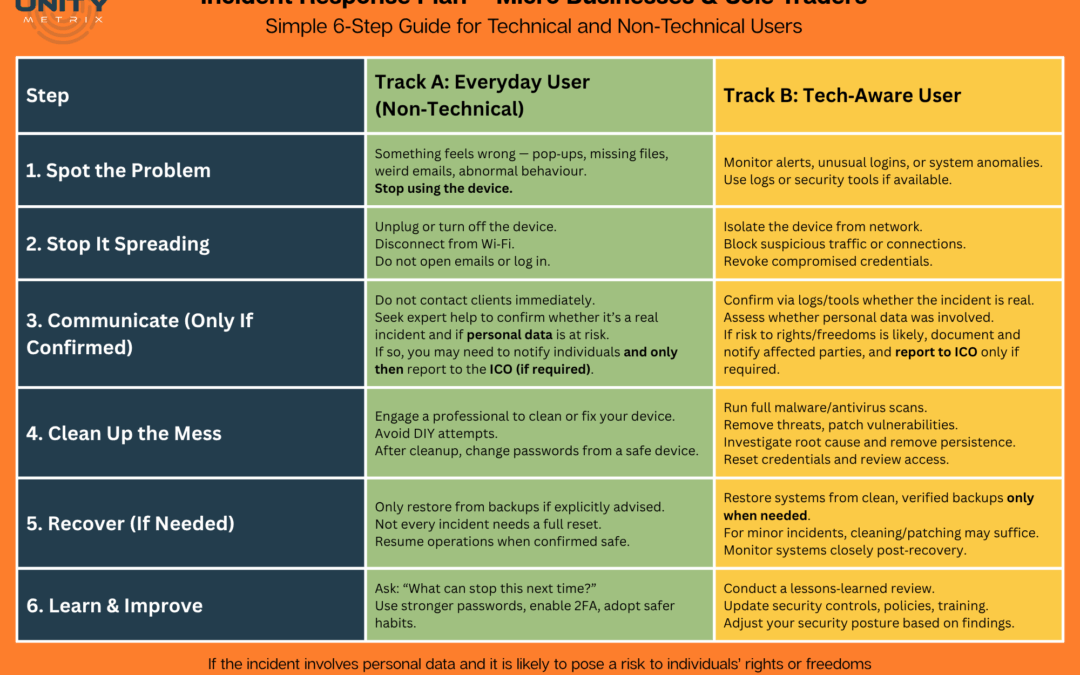
Casting a Wider Net: Automated Phishing Testing and End-User Training with Unity Metrix
Unity Metrix understands these challenges and offers a comprehensive solution tailored for your unique needs. Our service is more than a technology; it’s a commitment to keeping you safe.
Discover Unity Metrix’s Automated Phishing Testing and Training – Your anchor in the stormy seas of the digital world. Stand strong, stay safe.